SHA1:
- 4d465e4f36f82fa2489d2f582ee3a20cb2c17e32
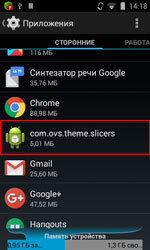
A Trojan for Android that is implemented as a service utility performing a set of simple functions. For example, it monitors the RAM consumption and terminates running processes if necessary. It also allows to control wireless connections, configure the screen brightness, and so on. Nevertheless, it is mainly designed to display advertisements.
Android.Slicer.1.origin is installed on the system by other software programs. This Trojan does not create a shortcut on the screen so that the user cannot launch the application by themselves.
Once Android.Slicer.1.origin is launched, or once the home screen is turned on or off, or the Wi-Fi module is disabled, the Trojan sends information regarding
- MEI identifier of the infected device
- MAC address of the Wi-Fi adapter
- Name of the device manufacturer
- OS version
The command and control (C&C) server, in its turn, replies with the following instructions:
- Add a shortcut to the home screen
- Display an advertisement
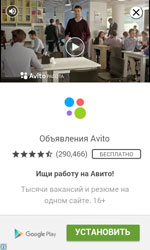
- Open advertising webpages in the browser or in a Google Play application
In addition, Android.Slicer.1.origin automatically installs free Google Play applications and buys paid-for ones. This function can be executed if the /system/bin catalog contains a file named .run-us, which is a Trojan—Android.Rootkit.40—similar to the SU utility.)
For that, Android.Slicer.1.origin opens a section in one of the specified applications and runs a standard uiautomator utility, designed to test GUI, with root privileges using Android.Rootkit.40. Then, with the help of this utility and the “uiautomator dump file_name” command, the Trojan creates an XML file that contains information about all the windows and interface elements displayed on the screen at the moment.
Then the Trojan searches for the following indentifiers:
- com.android.vending:id/buy_button (“Buy” and “Install” buttons);
- com.android.vending:id/continue_button (“Continue”).
After that, the Trojan uses the “input tap X Y” command (where X and Y are the coordinates of the middle of the button) and starts tapping the button until it disappears from the screen. Thus, the malware program can install any software program on Google Play. However, it can work only on mobile devices running Android 4.3, because Android 4.3 and later have the identifiers of the necessary buttons, and Android.Rootkit.40 cannot operate on devices with SELinux (Android 4.4 and later.)