SHA1: df17d83d81b8d2e3b45cf0759d29fdd5340bdfe4 (packed)
8c26ac74112c633ffda72752c2d1c25e37b24e40 (unpacked)
A malicious program designed to install other applications on the infected computer without user knowledge. When packed, the Trojan is about 3.5 MB in size; when unpacked, its size is 400 KB. The executable file is linked to MSVCP60.dll and MSVCRT.dll.
Once launched, the Trojan replicates itself to the memory. Prior to running, its parameters are updated with command and control server addresses.
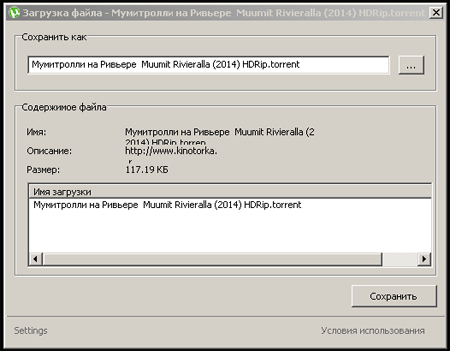
After that, the Trojan starts gathering information about the infected computer (OS version, computer name, user name, and so on) saving it to the structure in JSON format (JavaScript Object Notation). Subsequently, this data structure is used to retrieve a configuration file. Command and control servers allow Trojan.InstallCube.339 to download the payload only if the infected computer has a Russian IP address. While connecting to a command and control server, the Trojan displays the load indicator and, after that, demonstrates a dialog with information on the downloaded object. At that, the dialog supposedly belongs to the well-known mTorrent application.
If the user clicks the hardly visible Settings link at the bottom of the window, the Trojan will display the list of additional programs to be installed on the compromised computer.
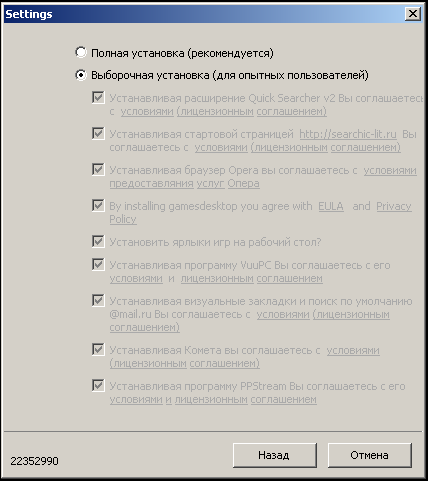
However, if the user clicks Save (“Сохранить”) in the previous dialog, then all the additional components will be downloaded together with the chosen file. Once Trojan.InstallCube.339 preforms its task, it removes itself.
Communication with command and control servers is carried out using User-Agent: "IC Loader 4.2.2". To initiate the connection, Trojan.InstallCube.339 sends the getToken request to the server and gets GetSettings as a reply. Once the GetSettings command is executed, the Trojan sends the server the ReportStart request. In reply, it receives data on affiliate software to be downloaded.