Packer: absent
Compilation date: absent
SHA1 hash:
- 12497d7c24011078cce12100f57a1cf368a3b17f
Description
RAT malware that operates in the 32-bit and 64-bit versions of Microsoft Windows operating systems. The studied sample is an MSI package with pre-configured remote control parameters to silently install the Remote Utilities software. It spreads within the malicious RAR-archive via phishing link. The backdoor is designed to remotely control the infected computer.
Operating routine
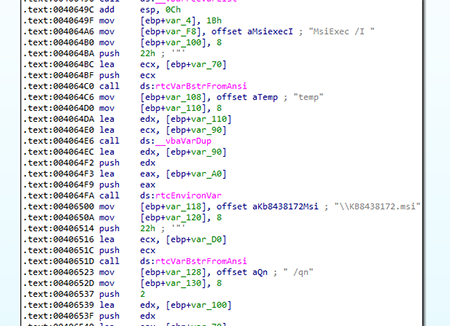
It is launched by a dropper that stores the installation archive in the resources section under the name LOG. The dropper saves the MSI package to the %TEMP% directory as KB8438172.msi and then launches it using the msiexec.exe installer. The dropper contains the source path — C:\Users\Kelevra\Desktop\Source\Project1.vbp.
The backdoor indicates it is ready for connection by sending a message to cerbe[@]protonmail[.]com.
This sample is notable for its distribution method. The victim receives a phishing email containing a link disguised as an important attachment.
The download link leads to
http[:]//ateliemilano[.]ru/stat/amsweb.php?eTmt6lRmkrDeoEeQB6MOVIKq4BTmbNCaI6vj%2FvgYEbHFcfWecHRVZGMpkK%2BMqevriOYlq9
CFe6NuQMfKPsSNIax3bNKkCaPPR0RA85HY4Bu%2B%2B6xw2oPITBvntn2dh0QCN9pV5fzq3T%2FnW270rsYkctA%2FwdvWH1bkEt2AdWnyEfaOwsKsSpyY
3azVX0D%2BKOm5.
From that address the victim is redirected to https[:]//kiat[.]by/recruitment/CV_Ekaterina_A_B_resume.rar, which is used to download the malicious archive.
ateliemilano[.]ru and kiat[.]by are actual websites, and the latter belongs to the recruitment agency. According to our information, they were repeatedly used for uploading trojans, as well as for redirecting requests to download malware.
Artifacts
During the investigation, we uncovered other compromised websites that distributed similar droppers with MSI packages. Some of them had the same redirect mechanisms as ateliemilano[.]ru. Some resources were allegedly used to upload trojans written in Visual Basic .NET (Trojan.GidraNET.1), which among other functionality, upload malicious droppers to compromised computers.