SHA1:
- 867e46870da05629f6930bccc969bab804950d81
The second version of the stealer Trojan is Trojan.PWS.Stealer.19490. Its self-designation is N0F1L3v2. It is written in С#. The Trojan is not packed.
As HWID the Trojan uses the serial number of the hard disk with the system partition. In the folder %TEMP% the stealer creates a folder with a name equivalent to HWID with nested folders called “Browsers”, “Wallets”, “Files” and “Directory”.
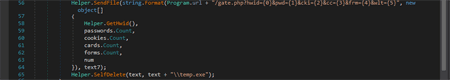
The Trojan steals cookies files, saved passwords, autofill data (including banking card numbers) from browsers Chrome, Opera, Kometa, Orbitum, Comodo Dragon, Amigo and Torch. The stolen information is written into files “Passwords.txt”, “Cookie.txt”, “CC.txt” and “Autofill.txt”.
It creates a copy of files stored on the Windows Desktop with the extensions TXT, DOC, DOCX, LOG in the subfolder “Desktop” of the “Files” directory created earlier. It creates a nested folder “FileZilla” in the folder “Files” created earlier. Then it tries to copy there files “%APPDATA%\\Filezilla\\filezilla_recentservers.xml” and “%APPDATA%\\Filezilla\\filezilla_sitemanager.xml”.
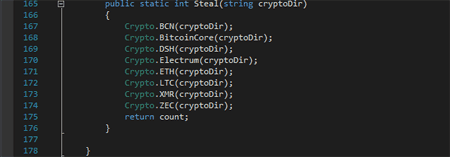
It tries to steal files of wallets of different cryptocurrencies and in case of success copies them into the folder created earlier and called “Wallets”:
Then all obtained data is packed into an archive and sent to the command and control server using the POST request.