SHA1:
- 803a0de1b2f4db33ec6c901d879ad267b63ab700
A loader Trojan that is usually spread by the miner Trojan.BtcMine.1541. It is written as an executable file Bot.exe.
Once launched, it creates its copy in the folder %APPDATA%\\Roaming\\Windows and provides its own autostart using the following methods:
- Creation of a task in the Windows Scheduler (task name is “\\System\\SecurityServiceUpdate”);
- Using the creation of an icon in the autorun folder;
- Modification of the registry key [HKCU\\SOFTWARE\\Microsoft\\Windows\\CurrentVersion\\Run] 'Webhost'.
When assembling the Trojan, the link to iplogger was indicated. It sends a GET request to the indicated address with the following User-Agent value:
- “Mozilla/5.0 (Windows NT 10.0; WOW64; rv:53.0) Gecko/20100101 Firefox/53.0”.
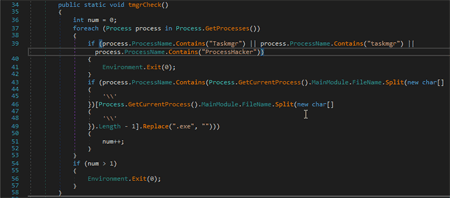
In a separate thread the Trojan goes through a list of launched processes. Once the processes with a substring "Taskmgr", "taskmgr", "ProcessHacker" are detected, or a string that matches the Trojan’s executable file is found, it shuts itself down.
A GET request is sent to the address stored in the Trojan’s body. The request looks the following way: “http://<cnc_addr>/?hwid=<hwid>”, where <cnc_addr> is the address of the command and control server, <hwid> is the serial number of the hard disk with the system partition. As a response to this request, the server can send a list of commands for execution. The commands are divided by the symbol “ | ”. The Trojan can execute two commands: update and download of an arbitrary file with its following launch.
If the Trojan receives an update command, it deletes the winhost.exe file from its folder and downloads a file to replace it via the link from the command. In case it obtains a second command, the Trojan downloads the indicated file and launches it.
Once the command is performed, the Trojan sends a GET request “http://<cnc_addr>/?hwid=<hwid>&completed=<c>”, where <cnc_addr> is the address of the command and control server, <hwid> is a serial number of the hard disk with the system sector, <c> is a parameter from the executed command.